At the beginning of 2020, remote working wasn’t even on the radar of most business owners. But fast-forward to 2021 and it’s become an integral part of our day-to-day business operations. And thanks to new and emerging technologies, it’s no longer seen as an obstacle to productivity and communication. In fact, for many remote workers, this new way of working has proven to be beneficial to their well-being and daily output. As a result, many IT managers and business owners are beginning to assess their existing processes and are even planning on deploying new remote working strategies for their post-pandemic way of working.
There are, however, a few security challenges that need to be overcome if you are planning on harnessing a remote working policy across your organisation. Traditionally, IT teams have had to manage, maintain and secure LAN (Local Area Network) environments, which is very different to how remote working environments are managed. Organisations now rely on the use of VPNs (Virtual Private Networks) to access their enterprise network externally, meaning security is required outside of their premises.
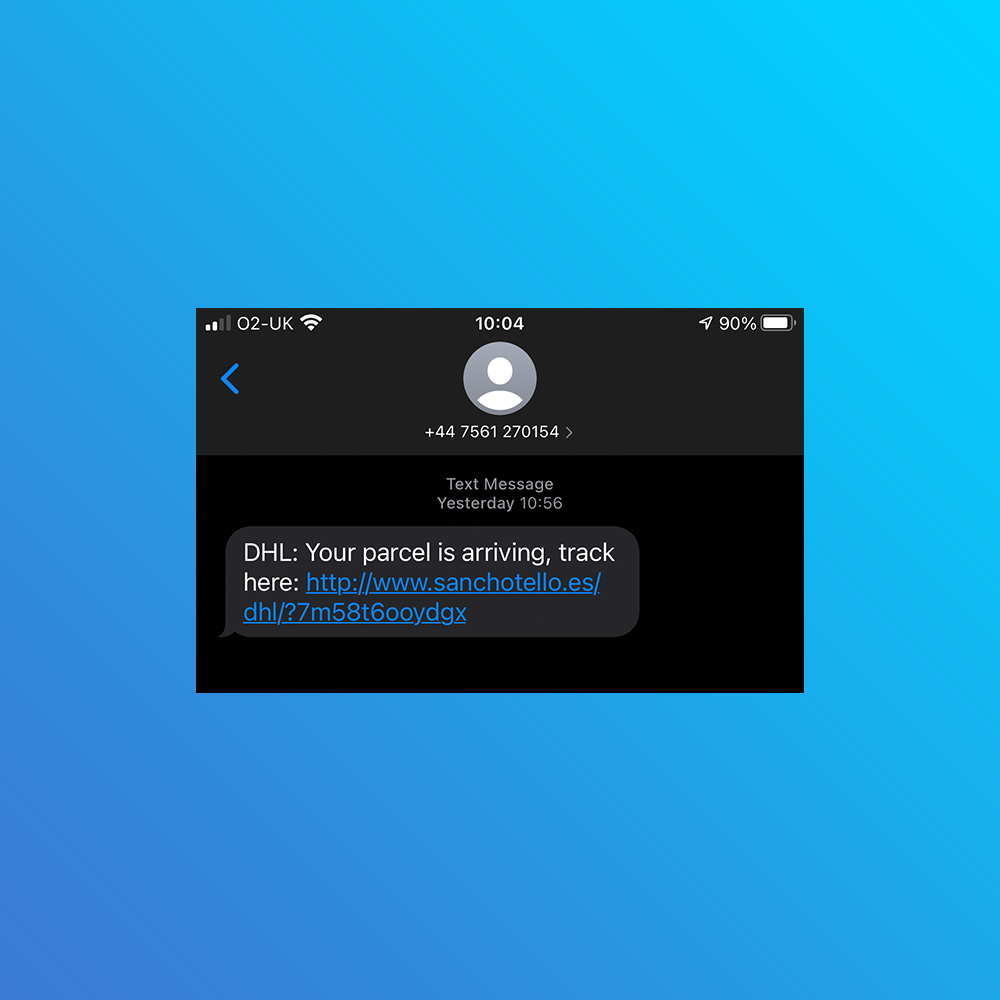
Although remote working technologies have moved forward over the last few years, so has cyber-crime. Attackers are now utilising much more sophisticated techniques to access sensitive company data, and with the sudden influx of remote workers in 2020, additional vulnerabilities in company devices and processes have emerged. In fact, we are now seeing more compromised end-user devices and phishing attempts on remote workers than ever before. But why?
The reason behind this surge in cyber-crime is down to the sheer number of people working from home, which has grown exponentially in 2020. Inevitably, home working environments aren’t designed for the sole purpose of working; these localised networks also contain a concoction of shared accounts and highly insecure personal devices. Cyber criminals use these environments as a platform to gain access to your sensitive company data. As a consequence, businesses now face a new series of challenges to secure their remote working operations and to combat the growing threat cyber-criminals impose on their networks.
Our top tips for a secure remote working environment
We’ve put together our top tips to help you ensure your remote working operations, and therefore sensitive business data, are effective and secure.
Educate your workforce
When it comes to securing your sensitive business data, the first step to take is educating your employees. Ensuring your remote workforce is aware of the techniques cyber-criminals use to compromise your network, what steps they need to take if they become a victim of cyber-crime, and why these steps need to be taken, should be your number one priority.
The easiest way to educate your workforce is by issuing a handbook containing best practices, including the use of two-factor authentication, and the importance of using a VPN. You could also consider deploying an Acceptable Use Policy (AUP), outlining what apps, websites and networks should and shouldn’t be used for accessing data.
Apply permission levels
Although a one-size-fits all approach to corporate network access may simplify data management, it could increase your vulnerability to potential security risks, especially when it comes to remote working. We’d recommend that you define and apply comprehensive corporate policies to assign network access levels across each member of your team. It’s important you find a happy medium between user access management and secure, remote access to your on-premise resources, hybrid cloud environments and the business applications using your policies.
As a managed service provider, DuoCall can help you plan and roll out the comprehensive policies you need to maximise security across your remote workforce. Talk to our team for more information.
Allow productivity, security and flexibility to work hand-in-hand
In order for your business to run as smoothly in a remote format as it would in a traditional office environment, balancing security with accessibility is key. You should consider how a globalised and secure remote access platform could help your team members gain access to their key data and applications remotely, without experiencing any latency issues and ensuring maximum productivity.
You also need to consider how flexible your remote working solutions are. If you are likely to increase the number of remote users in your workforce, you should look for a flexible, simple, per-user commercial model to futureproof your remote operations.
Prioritising remote worker security
IT managers and business owners have no control over the home Wi-Fi networks their remote employees are using to access company data. For this reason, it is paramount that robust security measures are implemented correctly. Businesses must treat all remote users with zero trust to enable a more secure approach to remote working.
By treating end-users with zero trust, businesses can utilise the cloud, allowing remote employees to access all the data they need from wherever they are. Companies can make use of Zero-Trust Network Access (ZTNA) architectures to ensure only authenticated users, devices and applications are able to access corporate data remotely. As a result, network access security is established and users can access company data from their preferred business devices and applications, including BYOD.
Businesses can also take remote working security to the next level with a Secure Access Service Edge (SASE) network architecture. SASE provides your remote workers with fast and efficient access to company data and resources from anywhere, whilst maintaining a zero trust model. What’s more, Software-Defined Wide Area Networking (SD-WAN) can be integrated with SASE seamlessly to provide improved efficiency, security and bandwidth.
If you’re looking for a managed service provider with networking and security expertise, please don’t hesitate to talk to our team of specialists. We would be more than happy to offer our advice and recommend the necessary products and services if you’re looking to maximise security across your network.