- Keep regular backups of critical business data
- Make sure all software is up to date
- Implement a password policy
- Put procedures in place to protect you from fraud
- Only connect devices to secure networks.
Unfortunately, recent research shows that only half of all businesses do all five of these tasks. About a third are connecting to unsecured Wi-Fi.
Cyber essentials
The Cyber Essentials Scheme is a Government scheme that helps organisations to guard against the most common cyber threats from the internet and demonstrate commitment to cyber security. It covers five main technical controls which will protect companies against an estimated 80% of common internet threats. The controls are:
- Secure your Internet connection (Firewalls and routers)
- Secure your devices and software (Secure configuration)
- Control access to your data and services (Access control)
- Protect from viruses and other malware (Malware protection)
- Keep your devices and software up to date (Software updates)
For more information about how to get certified visit the National Cyber Security Centre (NCSC): www.ncsc.gov.uk/cyberessentials
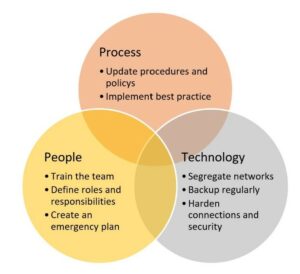
Figure 1 The headings: People, processes and technology is a good way to examine your business
Summary
By way of a summary, here is a checklist. Can you tick all the boxes?
| Backups | Done? | |
| Identify what data you need to back up | Information that your business couldn’t function without | |
| Keep your backup separate from your computer | Access to data backups should be restricted so that they are not accessible by staff and are not permanently connected | |
| Consider using cloud storage | A service provider stores your data on their infrastructure, so it is physically separate from your location | |
| Regular process | Make running a backup part of your everyday business. | |
| Malware | ||
| Install antivirus software
|
Make sure it is switched on | |
| Block unknown apps
|
Prevent staff from downloading them | |
| Keep all IT equipment up to date
|
Software and firmware is the latest versions | |
| Control how USB drives and memory cards can be used | One device containing malware could devastate your business | |
| Switch on a firewall
|
This creates a buffer between your network and the Internet. | |
| Equipment | ||
| Password protection
|
Use a suitably complex PIN or password on all equipment | |
| Stolen devices
|
Ensure if lost or stolen, devices can be tracked, locked or wiped | |
| Keep your software up to date
|
This includes operating systems as well as apps | |
| Don’t connect to unknown Wi-Fi hotspots | There is no way to easily find out who controls them | |
| Passwords | ||
| Switch on password protection
|
And use a screen lock password, PIN, or other method such as fingerprint or face recognition | |
| Use two factor authentication (2FA) when available | It adds a lot of security for not much effort | |
| Don’t use predictable passwords
|
They should be easy to remember, but hard to guess | |
| Help staff cope with ‘password overload’ | Do not enforce regular password changes, they only need to be changed if you suspect they are compromised | |
| Change default passwords | A very common error is keeping default usernames and passwords that equipment is issued with | |
| Phishing | ||
| Reduce impact of a successful attack | Configure staff accounts to the lowest level of user rights required for their jobs. If they are victim to a phishing attack, potential damage is reduced | |
| Think about how you work | How could someone target your business? Make sure your staff understand the normal way of working | |
| Check for the obvious signs of phishing | Many frauds originate overseas and often the spelling, grammar, punctuation and graphics are poor | |
| Make sure all attacks are reported | Encourage your staff to ask for help if they think that they might have been a victim of phishing. |
Automechanika 2023
Automechanika Birmingham will return to the NEC on 6-8 June 2023. Cybersecurity will be an important part of the seminars and presentations. Come and learn more from a range of industry experts and exhibitors. You can book your FREE ticket here.